hmm, it’s a weird topic to write blog on. Because Cyberpanel comes with a built in Certbot, and can automatically detects www and without www to install SSL for. Then why am I writing this up? All because I found a VPS client today facing the issue. Even though, Cyberpanel was telling me that the SSL is issued, it was only issued for non-www domain, but the www domain left behind. Let’s see how can we resolve this.
First problem
First problem came up when I tried to discover the Cyberpanel certbot binaries.
[root@server-sg /]# find . -name "certbot" ./usr/local/CyberCP/bin/certbot ./usr/local/CyberCP/lib/python3.6/site-packages/certbot ./usr/local/CyberPanel/bin/certbot ./usr/local/CyberPanel/lib/python3.6/site-packages/certbot [root@server-sg live]# /usr/local/CyberCP/bin/certbot --version certbot 0.21.1 [root@server-sg live]# /usr/local/CyberPanel/bin/certbot --version certbot 0.21.1
Both of the certbot I could find from Cyberpanel was very old, Certbot has 1.4 version in the Epel which has support for Acme 2 challenge, while the one that Cyberpanel is using doesn’t. I hence decided to install a certbot for our case:
yum install epel-release yum install certbot
These should be it for the latest version of certbot to start working in your Cyberpanel host. Once done, you may now generate the SSL using the following:
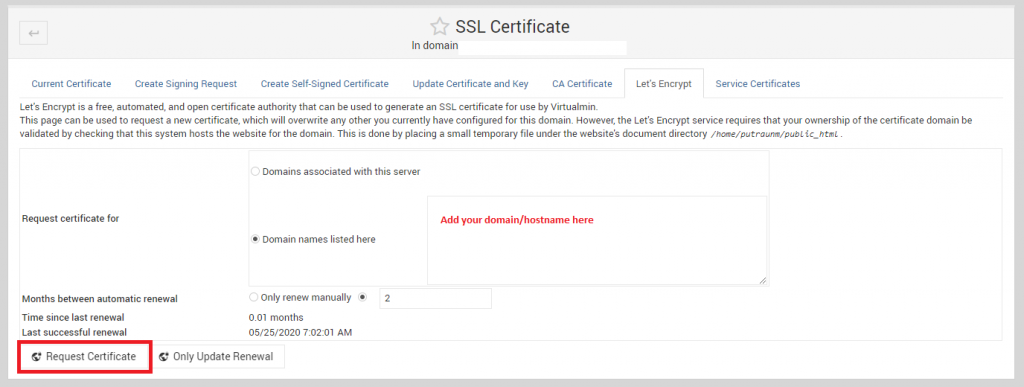
certbot certonly --webroot -w /home/yourdomain.com/public_html -d yourdomain.com -d www.yourdomain.com
Remember to replace yourdomain.com with the actual one that is having problem with. Cyberpanel creates the home directory with the primary domain, so the remember to give the correct document root for the value of attribute ‘-w’.
Once this id done, certbot should automatically verify the challenge and get the issued license for you. Lets encrypt license are usually stored at the following directory:
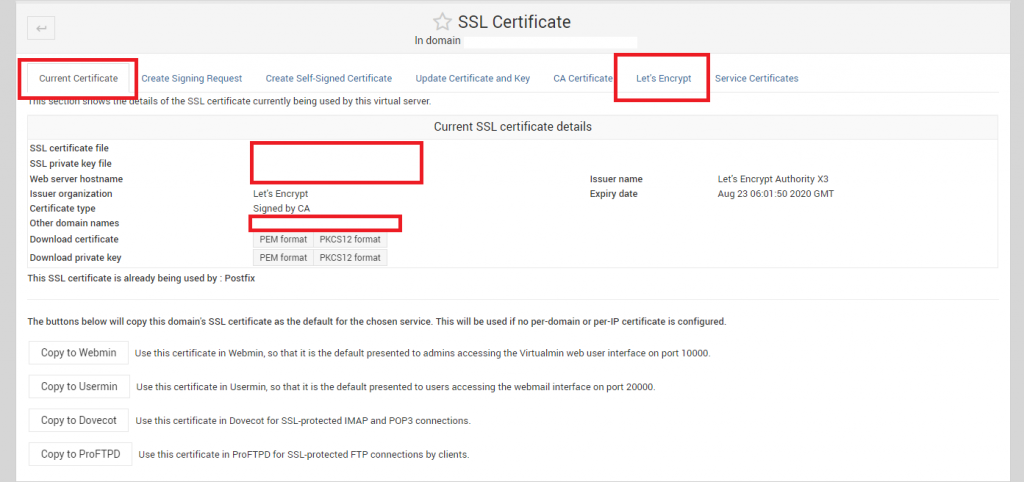
/etc/letsencrypt/live/yourdomain.com/ Files are: /etc/letsencrypt/live/yourdomain.com/privatekey.pem /etc/letsencrypt/live/yourdomain.com/fullchain.pem
If you had already created the SSL using Cyberpanel (which you must have done if you viewing this post), then remember, certbot will place the SSLs in /etc/letsencrypt/live/yourdomain.com-001/ folder. The name of the folder would be shown at the time you complete issuing SSL with certbot.
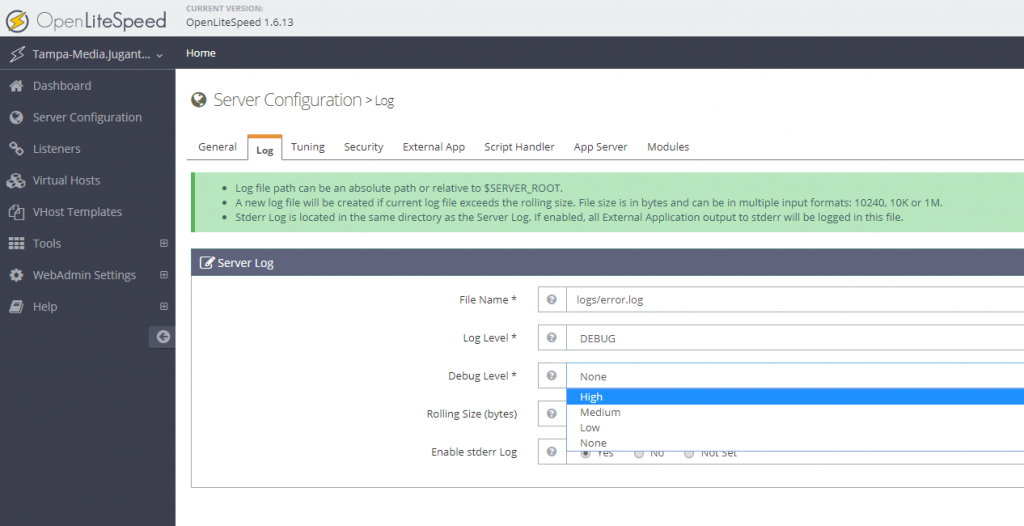
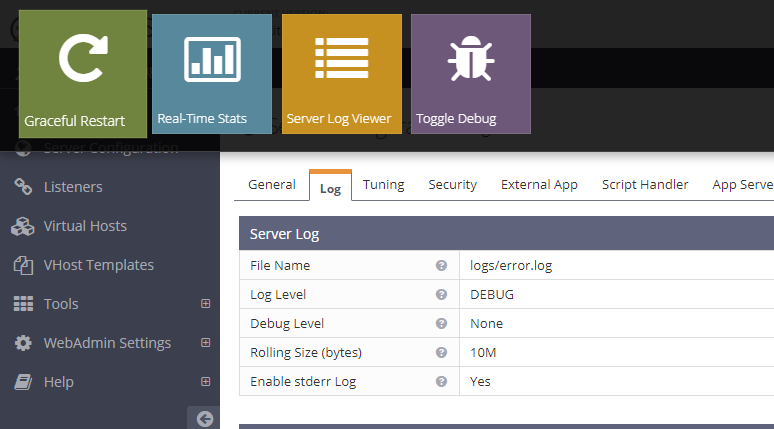
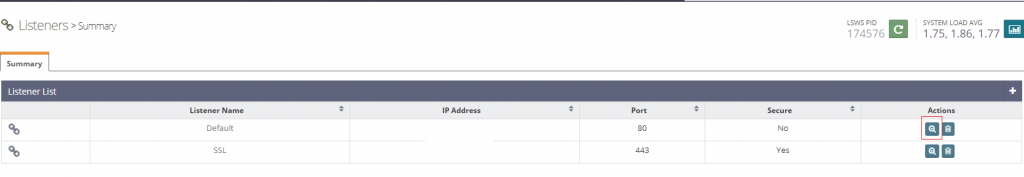
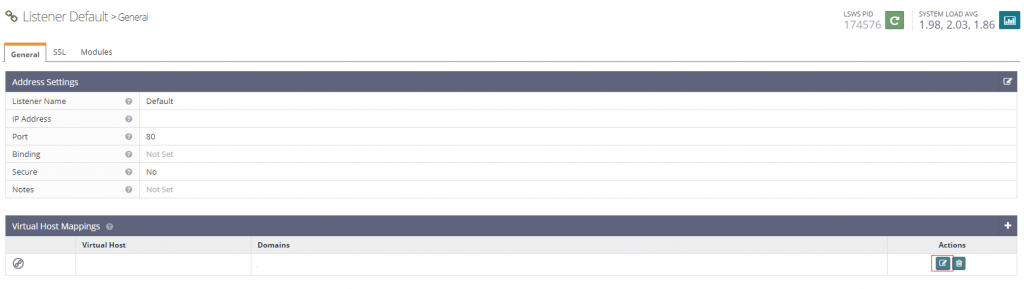
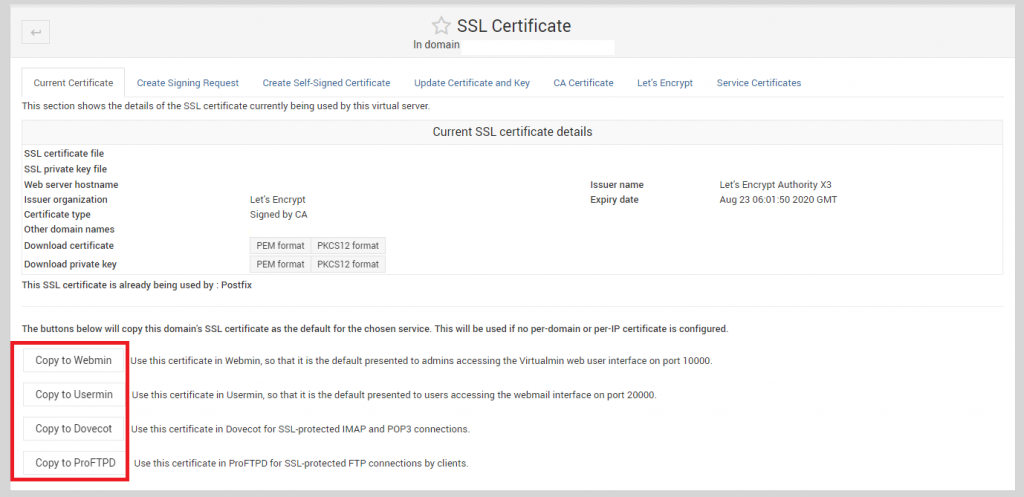
There are couple of ways you may use the SSL now. Either you may replace the old directory with the new, or just change the settings in either the vhost conf or the openlitespeed SSL settings. I find the easiest way is just to replace the old directory with the new. Something like this should work:
mv /etc/letsencrypt/live/yourdomain.com /etc/letsencrypt/live/old_yourdomain.com mv /etc/letsencrypt/live/yourdomain.com-001 /etc/letsencrypt/live/yourdomain.com
Once this is done, remember to restart your openlitespeed:
service lsws restart
Now your https on the WWW should work without any problem. If not, try clearing your browser cache and retry.